Google Cloud: Established actors are increasingly targeting backup

In addition to primary data, financially motivated threats are increasingly saboting cloud backups to maximize the leverage in blackmail systems, Google warned in its Cloud Threat Horizons H2 2025, which was published today.
These threat actors can deactivate backup routines, delete stored data, or change users’ authorization to block the restore attacks.
The most common way to infiltrate the threat to a cloud threat
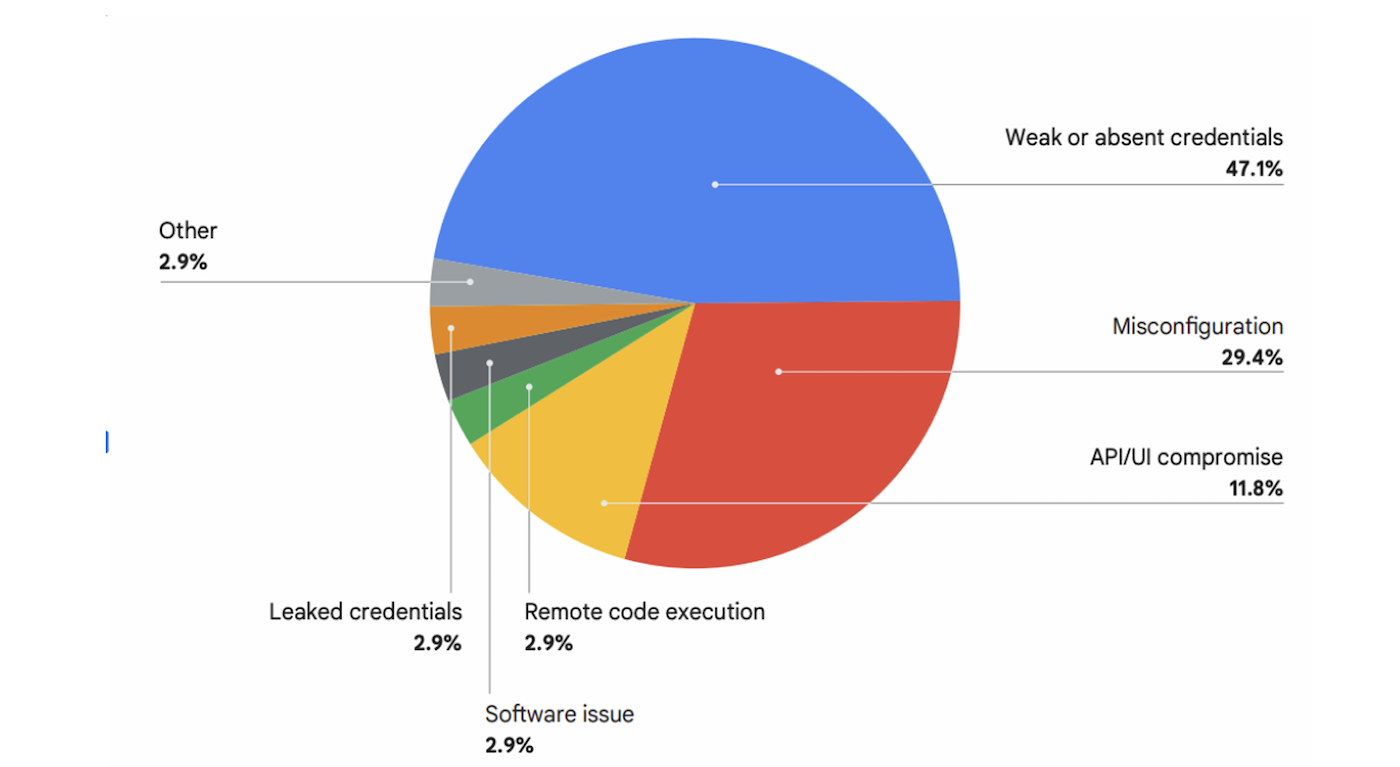
In the second half of 2025, a compromise represents 47% of cloud security incidents, while incorrect configuration followed 29%, according to Google Cloud. The leakage of login data – present in 2.9% of initial cases of access – also represent a growing question.
They said that sources of prevailing threats have been very similar to trends since the beginning of the year. The most common access points of weak or absent credentials, incorrect configurations and API or UI compromise.
Malware delivery via cloud services also grows
Google Cloud identified these other trends of cyber security threats:
- Social engineering and MFA bypass are still a common tactic to access the cloud’s surroundings.
- PDF Decoy hosted on legitimate cloud platforms are used to deliver malware.
- Cloud services such as Google Disk, SharePoint, Dropbox and Github are abused to host infected PDFs.
- Access through incorrect configurations has decreased by 4.9%.
- API/UI -based approach has fallen by 5.3%.
In two important cases, the North Korean state sponsored by actor-Kirty Google Cloud calls an UNC4899-nichel to cryptocurrency and blockchain industry with attacks that began as social media engineering, and ended the attackers to withdraw cryptocurci. In both cases, the attacker has been submitted to seek freelance opportunities for software development, in one case on LinkedIn and the other on a telegram.
Proven procedures: Secure access and monitoring suspicious file behavior
Google Cloud recommended the following defense strategies for cloud security teams:
- Use controls for identity and access management (IAM), manage proactive vulnerability and regularly audit permission.
- Observe the leak of login data using automated detection tools.
- Robust program of vulnerability and patch management.
- Monitor PDF files or readers of the command and scripting interpreters such as Powershell.exe, and files stored in Tempders trying to connect to cloud storage or opening.
- Separate authorization to sign from permission to uploader.
- Stay in readiness for .Desktop files that are used as a boobytrapped PDFS, use them as droplets in displaying harmless PDF simultaneously.
“Although there is no single silver missile, the data is that mastering the foundations provides the most important investment,” said Crystal Lister, security advisor to Google Cloud Security, in -mail of Techrepublic. “The huge percentage of violations, more than 76% according to our latest research, begin foundations such as weak credentials and incorrect configurations. Before focusing on sophisticated nation -state actors, ensure that you have strong identity and approach and robust security.”
Cloud backup segmentation can reduce risk
Google Cloud has also proposed to separate the production and backup infrastructure based on cloud by designing separate VPC networks for your production and backup. Backup data can be replicated across the geographical surroundings through conventional cloud services.
Reading our tips for 7 best selections of software for encryption in 2025.
